Cloud evolution can be considered synonymous to banking system evolution. Earlier people used to keep all their money, movable assets (precious metals, stones etc.) in their personal possessions and even in underground lockers as they thought that depositing their hard earned money with bank can be disastrous. Banking system evolved over the period of time. Legal and security process compliances protected by Law played a big role in making banking and financial systems trustworthy. Now, people hardly keep any cash with them. Most of us carry plastic money and transact digitally.
Cloud computing is also evolving the same way.
Robust cloud architecture with strong security implementation at all layers in the stack powered with legal compliances and government protection is the key to cloud security. As Banks didn’t vanish despite frauds, thefts and malpractices, cloud security is going to get evolved but as much faster rate. Digital world has zero tolerance for waiting! Evolution is natural and is bound to happen.
So what are the steps typically a cloud service provider should follow in order to secure its cloud?
Cloud is complex and hence security measures are not simple too. Cloud needs to be secured at all layers in its stack. Let’s briefly look into major areas.
At infrastructure level: A sysadmin of the cloud provider can attack the systems since he/she has got all the admin rights. With root privileges at each machine, the sysadmin can install or execute all sorts of software to perform an attack. Furthermore, with physical access to the machine, a sysadmin can perform more sophisticated attacks like cold boot attacks and even tamper with the hardware.
Protection measures:
- No single person should accumulate all these privileges.
- Provider should deploy stringent security devices, restricted access control policies, and surveillance mechanisms to protect the physical integrity of the hardware.
- Thus, we assume that, by enforcing a security processes, the provider itself can prevent attacks that require physical access to the machines.
- The only way a sysadmin would be able to gain physical access to a node running a costumer’s VM is by diverting this VM to a machine under his/her control, located outside the IaaS’s security perimeter. Therefore, the cloud computing platform must be able to confine the VM execution inside the perimeter, and guarantee that at any point a sysadmin with root privileges remotely logged to a machine hosting a VM cannot access its memory.
- TCG (trusted computing group), a consortium of industry leader to identify and implement security measures at infrastructure level proposes a set of hardware and software technologies to enable the construction of trusted platforms suggests use of “remote attestation” (a mechanism to detect changes to the user’s computers by authorized parties).
At Platform level:
Security model at this level relies more on the provider to maintain data integrity and availability. Platform must take care of following security aspects:
- Integrity
- Confidentiality
- Authentication
- Defense against intrusion and DDoS attack
- SLA
At Application level:
The following key security elements should be carefully considered as an integral part of the SaaS application development and deployment process:
- SaaS deployment model
- Data security
- Network security
- Regulatory compliance
- Data segregation
- Availability
- Backup/Recovery Procedure
- Identity management and sign-on process
Most of the above are provided by PaaS and hence optimal utilization of PaaS in modeling SaaS is very important.
Some of the steps which can be taken to make SaaS secured are:
- Secure Product Engineering
- Secure Deployment
- Governance and Regulatory Compliance Audits
- Third-Party SaaS Security Assessment
At Data level:
Apart from securing data from corruption and losses by implementing data protection mechanism at infrastructure level, one needs to also make sure that sensitive data is encrypted during transit and at rest.
Apart from all the above measures, stringent security process implementation should also be part of making cloud secure. Periodic audits should happen. Governing security laws should be amended with advent in technologies, ethical hacking and vulnerability testing should be performed to make sure the cloud is secure across all layers.
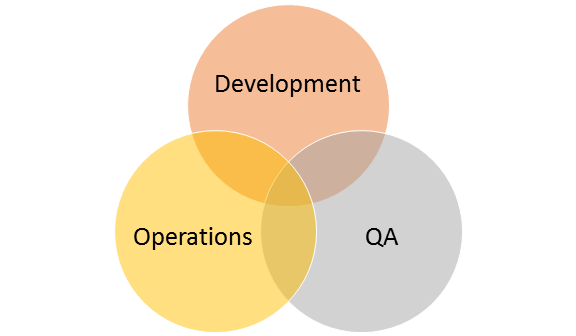
Author: Satish Agrawal is VP-Cloud Computing Practice at e-Zest Solutions Ltd. (www.e-zest.net) and mentor for Cloud Computing Professionals in and around Pune . His mission is to build core competencies at e-Zest in the domain of Cloud Computing for enterprises and ISVs and deliver best values. e-Zest's Cloud Computing Services provide complete cloud computing solutions from assessment to design to deployment to operation and adaption to evolution.



.jpg)
.jpg)